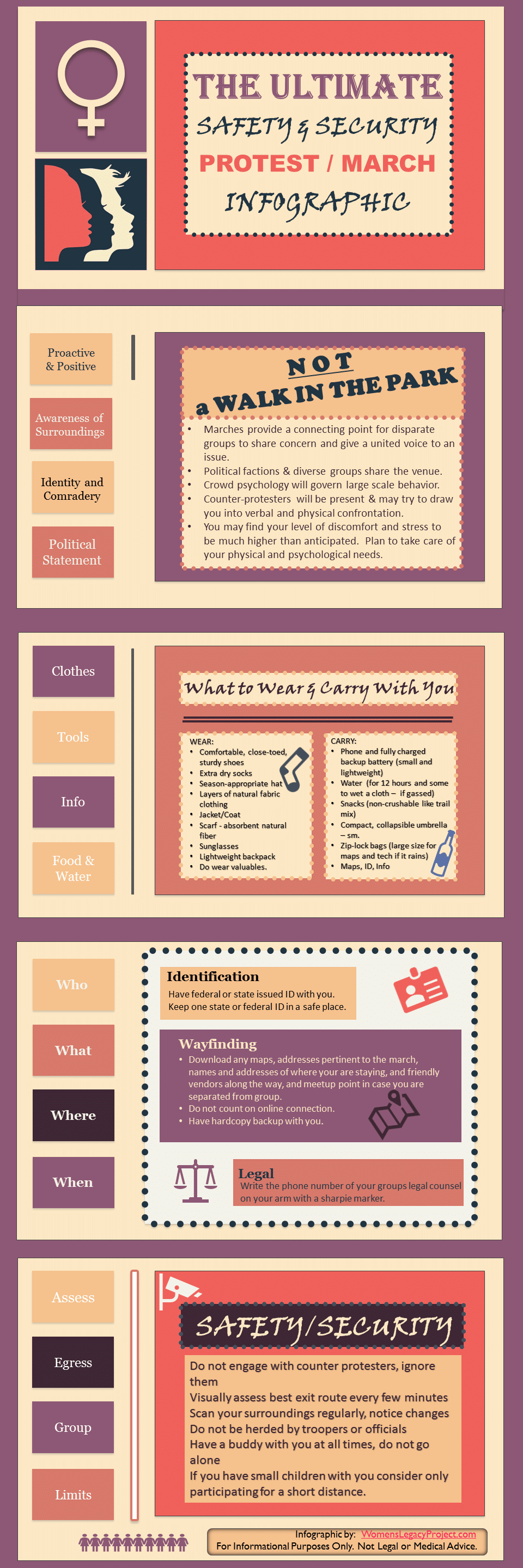
Created this infographic based on my years of protest with CodePink Women for Peace in DC and my years as a security manager at a major museum. Save the image or click for PDF .
Security Recommendations for Blogging
Here a Hack, There a Hack, Everywhere a Hack, Hack (Updated 2015 version) In this world where hacking seems to be de rigueur, it is becoming more and more difficult and important to have a secure blog. The attacks that began a couple years ago on WordPress sites left an especially sinister taste in my mouth. […]
My Annual BlogHer Logistics Post – #BlogHer14
As I have said before, “Prepare now so you can seem effortlessly organized later.” The secret to success seems to lie in being organized enough to take advantage of what the moment offers. At a conference, such as BlogHer, this means knowing where everything is. No, not knowing where all the junk you brought and […]
Heartbleed and Your Blog Security
A massive security bug in Open SSL has left more than half of the internet’s site vulnerable to data breaches. Here I share one suggestion for finding out if you blog is safe.
Self-hosted Blog cPanel Security Tips
Yesterday I covered some basic security tips for WordPress blogs. Today I am covering some of the very basic things you can do to make your site or blog more secure cPanel, the panel through which you set up the basic self-hosting service particulars of your site. I am not a computer programmer or software […]
Is WordPress Security Oxymoronic?
Security again… sigh. I am trying to figure out how to ip deny certain ip addresses from visiting (read: hacking) my blog as a bit of preventive security. I spent a couple hours yesterday cutting and pasting ip addresses from my cpanel stat files into an excel spread sheet so I could easily cut and […]